2022 Jeep Grand Cherokee L Limited on 2040-cars
Clinton, Illinois, United States
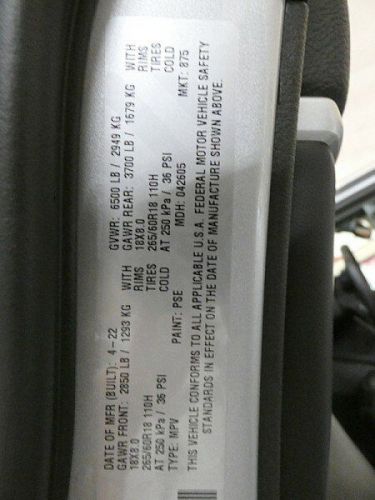
Engine:3.6 L
Fuel Type:Gasoline
Body Type:Sport Utility
Transmission:Automatic
For Sale By:Dealer
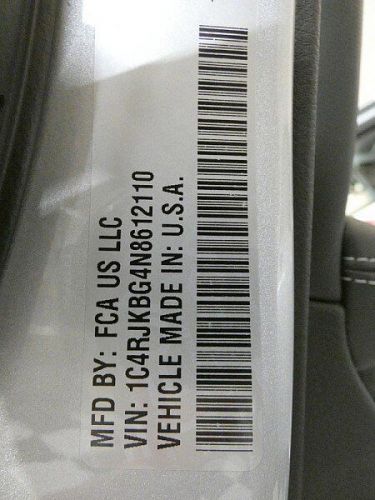
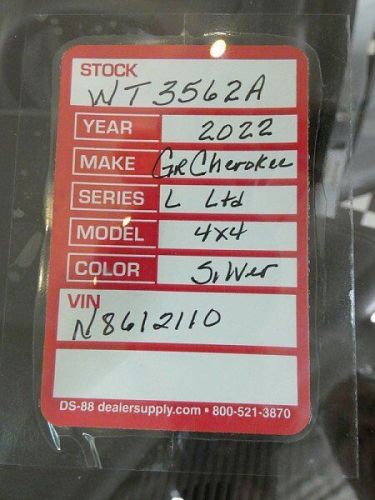
VIN (Vehicle Identification Number): 1C4RJKBG4N8612110
Mileage: 29163
Make: Jeep
Model: Grand Cherokee L
Trim: Limited
Drive Type: Limited 4x4
Number of Cylinders: 6
Features: ENGINE: 3.6L V6 24V VVT UPG I W/ESS
Power Options: --
Exterior Color: Silver
Interior Color: Black
Warranty: Unspecified
Jeep Grand Cherokee L for Sale
 2024 jeep grand cherokee l limited(US $50,988.00)
2024 jeep grand cherokee l limited(US $50,988.00) 2022 jeep grand cherokee l limited 4x4(US $36,860.00)
2022 jeep grand cherokee l limited 4x4(US $36,860.00) 2021 jeep grand cherokee l limited sport utility 4d(US $37,095.00)
2021 jeep grand cherokee l limited sport utility 4d(US $37,095.00) 2022 jeep grand cherokee l limited 4x4(US $27,877.50)
2022 jeep grand cherokee l limited 4x4(US $27,877.50) 2024 jeep grand cherokee l laredo(US $42,083.00)
2024 jeep grand cherokee l laredo(US $42,083.00) 2021 jeep grand cherokee l limited 4x4(US $35,619.00)
2021 jeep grand cherokee l limited 4x4(US $35,619.00)
Auto Services in Illinois
Waukegan-Gurnee Auto Body ★★★★★
Walker Tire & Exhaust ★★★★★
Twin City Upholstery ★★★★★
Tuffy Auto Service Centers ★★★★★
Top Line ★★★★★
Top Gun Red ★★★★★
Auto blog
Jeep gives a trio of customs an encore showing at SEMA
Wed, 05 Nov 2014While Jeep certainly had some new customs on display at this year's SEMA show, it wasn't afraid to recycle a few that people might have missed from earlier this year. The maker of many beloved off-roaders already displayed the Jeep Cherokee Dakar, Maximum Performance Wrangler and Wrangler Mojo at the 2014 Easter Safari, but they all made it to SEMA for an encore.
Based around the Trailhawk, the Cherokee Dakar (pictured above) imagines an even more off-road-capable version of the crossover. The concept wears a mix of Silver Steel Stain paint with Flame Red graphics and rides on 17-inch wheels wrapped in 33-inch BFGoodrich Mud Terrain tires. To back up the rugged look, the Dakar is fitted with rock rails and skid plates protecting the oil pan, front suspension, fuel tank and other underbody parts. It also sports prototype parts from Jeep Performance Parts, including a lift kit and fender flares.
The Wrangler is one of the paragons of off-roading, and as the name suggests, the Maximum Performance Wrangler concept is meant to be the ultimate example of what it can do. The custom features locking Dana 60 axles front and rear, a 4:1 Rock-Trac transfer case, prototype 4-inch lift kit and 37-inch Mud Terrain tires over beadlock wheels. To stay on the trails well into the night, a bar of LEDs is mounted above the windshield. And finally, the Mopar Blue exterior kind of makes the vehicle look like the world's toughest blueberry.
Best 3rd Row SUVs of 2024
Wed, Oct 19 2022If you plan on using a vehicle's third row a lot, let us at least make the suggestion that a minivan would be a smarter bet than anything you're going to see on this list of best three-row SUVs. Their third rows are bigger, more comfortable and easier to get to. The kids will definitely be happier. Here are our two top choices. OK, now that that's out of the way, we totally get why minivans are totally depressing and that if the kids want to be happier, they can buy their own darn vehicle. You're buying, you're driving, you're being seen in it and you'd rather have a three-row SUV. Fair enough. Luckily, there are more choices than ever and they're really good. The best do a particularly good job of being family friendly without looking like a drab transportation appliance, although really, you can't go wrong with any of the mainstream three-row SUVs. Now, some of the luxury choices are a bit suspect, including those that are otherwise very appealing but have cramped third-row seats (the Genesis GV80 comes to mind). We're focusing on three-row SUVs here, so having a usable third row is a must. In this list, we have broken things down into four sub-categories: Best Three-Row Crossover | Best Full-size Three-Row SUV Best Luxury Three-Row SUV | Best Flagship Luxury Three-Row SUV Note that we define crossovers as SUVs since most buyers use the terms interchangeably, but acknowledge that "crossover" is literally a vehicle with a car-like unibody structure as opposed to the truck-like, body-on-frame construction that traditionally has defined "SUV." In other words, we consider all crossovers SUVs, but not all SUVs are crossovers (specifically those in the full-size segment and some in the flagship luxury segment). Best Three-Row Crossover SUVs of 2024 2024 Honda Pilot Why it stands out: Exceptional storage and cargo space; unique second-row functionality; refined ride; versatile and capable TrailSport; advanced AWDCould be better: Subpar acceleration with lackadaisical transmission and engine response; so-so driver assistance tech Read our full 2024 Honda Pilot Review The Honda Pilot was completely redesigned for 2023. It maintains its predecessor's family friendly packaging and overall focus, but it has injected a welcome sense of style (especially in the TrailSport pictured above) that makes it stand out much better from the big crossover crowd.
Land Rover Defender V8 vs. Jeep Wrangler Rubicon 392 | V8 4x4s square off on paper
Thu, Feb 25 2021Land Rover pulled the sheet off its 2022 Defender on Wednesday, introducing another high-performance V8 to the off-road segment. This time, it's a 5.0-liter, supercharged V8 boasting 518 horsepower. It will be available in both the Defender 90 and 110 models. In the former, Land Rover says it can crack off a 0-60 run in just 4.9 seconds on its way to a top speed of 149 mph. The long-wheelbase 110 will be a bit slower, but "slow" probably isn't the right adjective to use here at all. But Land Rover isn't the only automaker offering a high-performance variant of its off-road SUV. While Jeep may have been sneered at for presenting the 2021 Wrangler Rubicon 392 on the heels of the 2021 Ford Bronco's introduction, it starts to make a lot more sense in this context. There's reportedly a high-output Bronco on the way, too, so call Jeep the dinosaur of the group all you want, but you can't put a price on being first. Well, you can, actually, but that's not the point. Thankfully, both Land Rover and Jeep have provided enough specs for us to rough out a comparison chart. Since the Rubicon 392 is offered only in four-door guise, we're looking at the long-wheelbase Defender 110 as its direct competitor here. Have a look: There are a few caveats to mention off the top. For starters, we don't have an official curb weight for the V8-powered Defender yet, as Land Rover has not finalized its U.S. specs. We used the European figures (as provided by a spokesperson), which we expect to be accurate within about 50 pounds. The 0-60 time provided by Land Rover was for the Defender 90, which is smaller and somewhat lighter than the 110. When equipped with the inline-6, the Defender 110 is about a tenth of a second slower to 60 than the Defender 90, so we figure it should be roughly the same for the V8. While the Defender has nearly 50 horsepower on the Wrangler, that advantage disappears thanks to the Land Rover V8's monster weight penalty, which will fall somewhere between 600 and 700 pounds depending on equipment. Yikes. On the flip side, however, the Land Rover has the edge in top speed, and it's not even close. Chalk that up to the tires, we suspect. We know for a fact that the Rubicon 392's all-terrains dictate its speed limiter; Jeep's own engineers told us as much. This could make for a (hypothetically) interesting drag race, as the Jeep's advantage off the line may evaporate once triple digits come into play.