2012 Chrysler 200 Touring on 2040-cars
1875 E Edwardsville Rd, Wood River, Illinois, United States
Engine:2.4L I4 16V MPFI DOHC
Transmission:Automatic
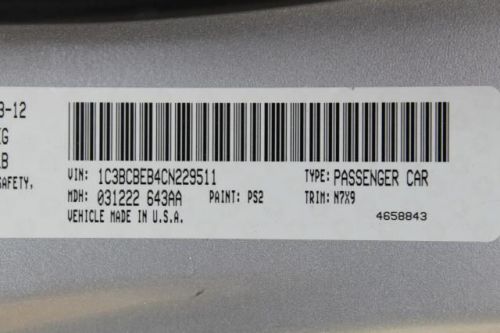
VIN (Vehicle Identification Number): 1C3BCBEB4CN229511
Stock Num: S1256
Make: Chrysler
Model: 200 Touring
Year: 2012
Exterior Color: Bright Silver Metallic
Interior Color: Black / Light Frost Beige
Options: Drive Type: FWD
Number of Doors: 2 Doors
Mileage: 35210
ATTENTION!!! SAVE BIG! The convertible you've always wanted! If you're looking for comfort and reliability that won't cost you tens of thousands then come check out this convertible today. This great 200 has been priced quite low, but still has comfort and safety to spare. CALL DAVID SANDERS FOR MORE DETAILS AND AVAILABILITY AT 855-518-5647!
Chrysler 200 Series for Sale
 2015 chrysler 200 c
2015 chrysler 200 c 2015 chrysler 200 s(US $27,584.00)
2015 chrysler 200 s(US $27,584.00) 2015 chrysler 200 s(US $24,959.00)
2015 chrysler 200 s(US $24,959.00) 2015 chrysler 200 c(US $31,022.00)
2015 chrysler 200 c(US $31,022.00) 2013 chrysler 200 touring(US $15,998.00)
2013 chrysler 200 touring(US $15,998.00) 2013 chrysler 200 touring(US $14,998.00)
2013 chrysler 200 touring(US $14,998.00)
Auto Services in Illinois
Waukegan-Gurnee Auto Body ★★★★★
Walker Tire & Exhaust ★★★★★
Twin City Upholstery ★★★★★
Tuffy Auto Service Centers ★★★★★
Top Line ★★★★★
Top Gun Red ★★★★★
Auto blog
Ferrari IPO could come any day now
Sun, Jul 12 2015According to Bloomberg, Fiat Chrysler Automotive Sergio Marchionne told reporters at the Toronto Global Forum that the Ferrari IPO could come any day now. "We are days away from filing the prospectus," said Marchionne, who declined to confirm whether rumors of involvement from UBS Group AG, JPMorgan Chase & Co and Goldman Sachs Group were accurate. In addition to an expected filing in New York, Marchionne hinted that a secondary filing could take place in Milan, Italy. Although the FCA Chief Executive didn't offer any expected sum for Ferrari, he had previously suggested that an IPO for the iconic Italian brand could be worth $1 billion, ringing the registers to the tune of 10 percent of the company's $11 billion valuation. According to Bloomberg, that potential sum is significantly higher than its own internal figures indicate after taking a poll of analysts who we assume must know a heck of a lot more about such things than we do. Considering how close we apparently are to the actual filing, though, we probably won't have to wait long to find out. Another hot topic any time Sergio is the subject of reporter questioning is a potential merger with General Motors or another large, full-line automaker. It seems there aren't any new revelations to reveal on the consolidation front, though Marchionne told reporters there were no plans to mount a hostile takeover of GM or any "other, less optimal" partners. Related Video: News Source: BloombergImage Credit: STR/AFP/Getty Earnings/Financials Chrysler Ferrari Fiat Sergio Marchionne FCA
Fiat Chrysler profit up as it closes in on retiring its debt
Thu, Apr 26 2018MILAN — Fiat Chrysler Automobiles reduced its debt by more than expected in the first quarter, putting the carmaker well on course to become cash positive later this year. Chief Executive Sergio Marchionne expects to cancel all debt during 2018 — possibly by the end of June — and generate around 4 billion euros ($5 billion) in net cash by the end of the year. Marchionne has said that forecast does not include any one-off measures, nor the impact of the planned spinoff of parts maker Magneti Marelli, which he hopes to execute by early 2019. The world's seventh-largest carmaker said on Thursday net debt had fallen to 1.3 billion euros ($1.6 billion) by the end of March, well below a consensus forecast of 2.6 billion euros in a Thomson Reuters poll of analysts. FCA said capital spending fell 900 million euros in the quarter due to "program timing," which analysts said implied higher investments for the rest of the year. The Italian-American group said first-quarter operating profit rose 5 percent to 1.61 billion euros, below a consensus forecast of 1.74 billion, as a weaker performance from its North American profit center weighed. Shipments there were higher due to the new Jeep Wrangler and Compass models. But currency moves hit revenues and earnings, and costs related to new product launches added to the pressure. FCA's shift to sell more trucks and SUVs boosted margins yet again in North America to 7.4 percent from 7.3 percent in the same quarter a year ago, although they were down from the 8 percent recorded in the preceding three months. Marchionne, preparing to hand over to an internal successor next year, is close to his goal of ending a margin gap with larger U.S. rivals General Motors and Ford. The 65-year-old has said becoming debt free and being able to compete on a par with U.S. peers would mean FCA no longer needed a partner to survive and could well succeed on its own. The CEO has previously said tying up with another carmaker would help to meet the huge costs in an industry investing in electric vehicles and automated driving. FCA shares fell immediately after the results, but recovered to trade up 3 percent at 19.71 euros by 1150 GMT, outperforming a 0.4 percent rise in Europe's blue-chip stock index. ($1 = 0.8214 euros) Reporting by Agnieszka FlakRelated Video: This content is hosted by a third party. To view it, please update your privacy preferences. Manage Settings.
FCA and UAW deal could mean huge production shakeups
Thu, Sep 17 2015The big labor contract between Fiat Chrysler Automobiles and the United Auto Workers is likely to lead to some very serious production shakeups across the company's North American manufacturing operations. That's according to a new report from Automotive News, which details the sweeping changes at no fewer than five production facilities in Michigan, Illinois, Ohio, Mexico, and Poland. So without further ado, here's what's going where, presented in easy to digest bullet form. Ram 1500 production would move from Warren, MI to Sterling Heights, MI Warren, MI would be retooled for unibody production and would handle the Jeep Grand Wagoneer and could potentially build Grand Cherokees to ease the strain on Detroit's Jefferson North factory Chrysler 200 production would move from Sterling Heights, MI to Toluca, Mexico Dodge Dart production would move from Belvidere, IL to Toluca, Mexic Fiat 500 production, which is currently handled by Toluca, would be concentrated in Poland, where the Euro-spec Cinquecento is built Jeep Cherokee production would move from Toledo, OH to Belvidere, IL to make room for Wrangler and Wrangler Pickup production Like we said, those are some big changes. But, as FCA CEO Sergio Marchionne said in an earlier interview with Automotive News, this kind of shakeup would make a lot of sense. In that August interview the exec said that automakers moved truck production to Mexico because they were "threatened" by the UAW. "The only thing [the UAW] want is to move the truck back. Which is right. If you move the truck back here, which is [the UAW's] domain, [and move] all the cars that we get killed on somewhere else, we could actually make sense of this bloody industry and actually increase the number of people employed in this country and really share wealth because we are making money," Marchionne told AN. News Source: Automotive News - sub. req.Image Credit: Bill Pugliano / Getty Images Plants/Manufacturing UAW/Unions Chrysler Dodge Fiat Jeep RAM Sergio Marchionne FCA toluca warren sterling heights